Cybersecurity Tools - Nmap
A beloved, real live movie star cyber tool
If there was such thing as a Cybersecurity Tools Hall of Fame, Nmap would be in it. It would likely be a rare unanimous choice, if this hall of fame followed the voting style that the NBA and Major League Baseball use. It is a long-time beloved and widely used tool for cybersecurity and IT professionals.
Widely used isn’t a good enough way to say it - universally might be a better fit. It is used by IT / network admins and cybersecurity analysts and engineers; for some on a daily basis. Nmap was created by and is still maintained and managed by Gordon Fyodor Lyon. This is a slice of the introduction to Nmap at nmap.org:
Nmap ("Network Mapper") is a free and open source utility for network discovery and security auditing. Many systems and network administrators also find it useful for tasks such as network inventory, managing service upgrade schedules, and monitoring host or service uptime.
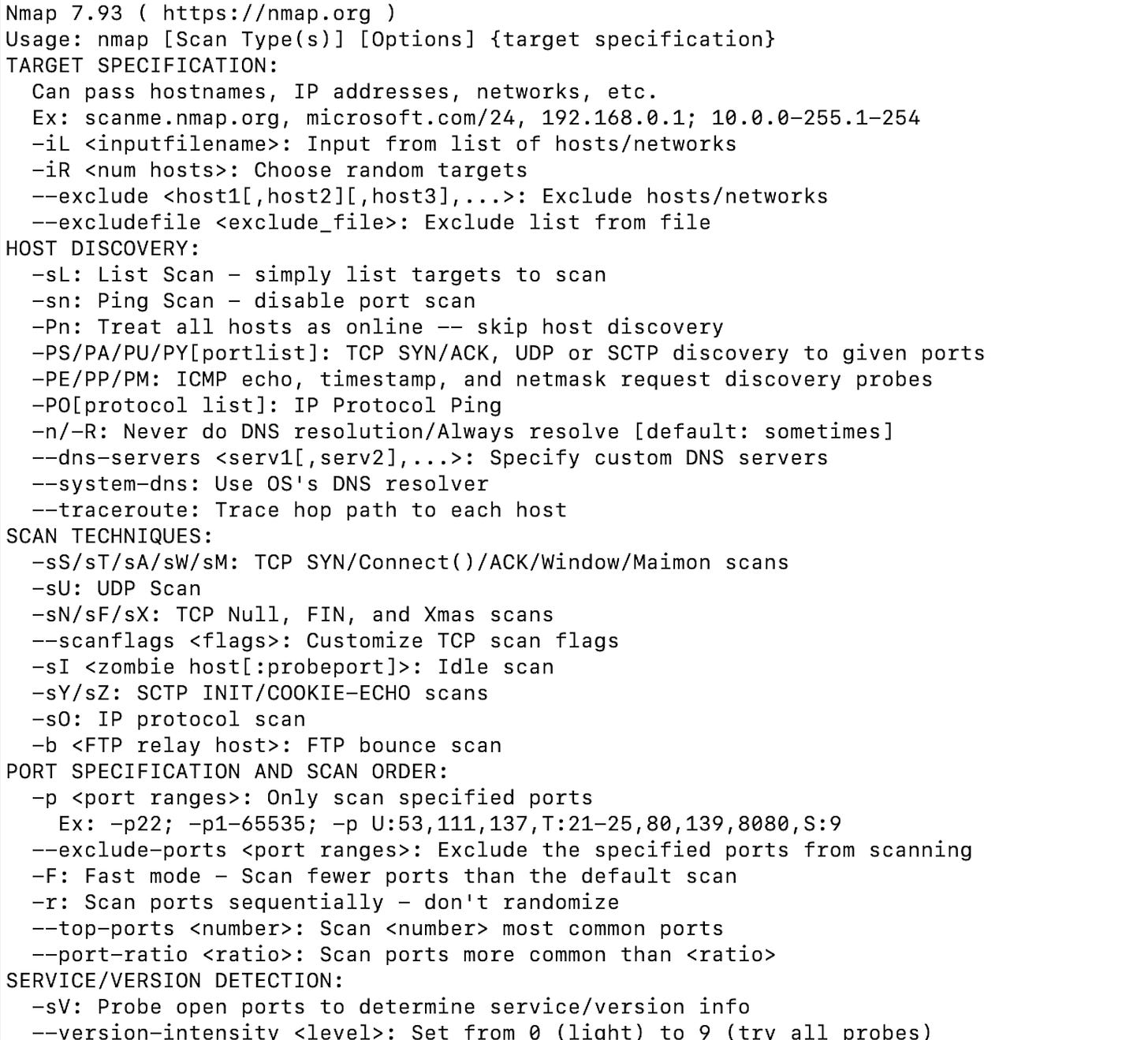
Nmap is a command line tool, and as soon as it’s launched it offers clear guidance on the ways to use it (syntax for commands):
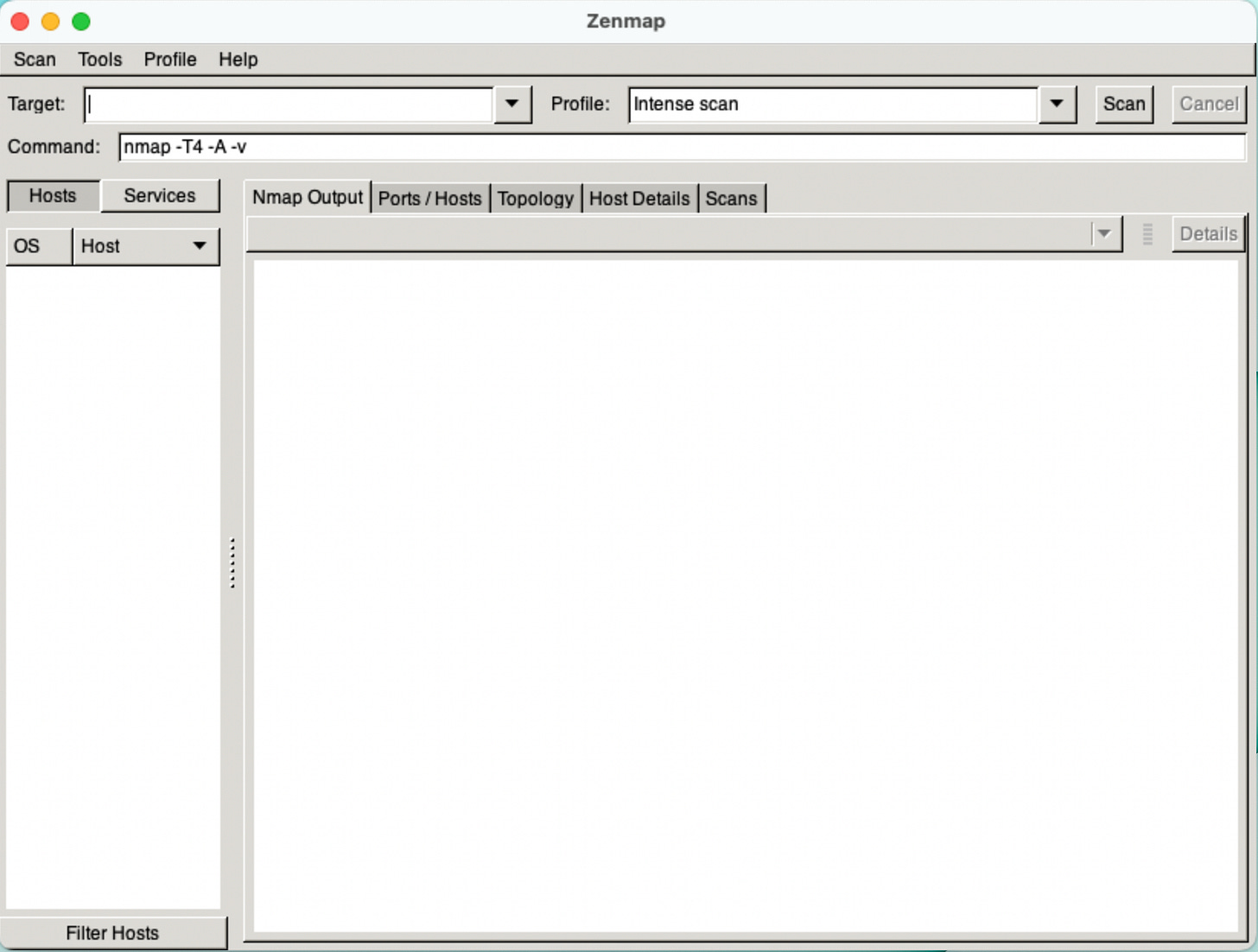
There is also a GUI (graphical user interface) version of Nmap - Zenmap.
Here are just a few of the ways that Nmap can be used:
Discovery Scanning: Identifying the hosts (computers, network devices, and all those allegedly smart IoT devices) that are running in our organization’s (or our home) environment
OS Fingerprinting: Identifying the operating system (and version) running on identified hosts
Seeing Active Ports and Services: Nmap can determine which ports and services (down to application name and version level) are active on the devices it discovers in our networks
Comparing Scan Results: Using the Ndiff utility.
All of these things are important and even essential when it comes to knowing what’s “alive” on our network, knowing what we have to defend on that network, and understanding the attack surface in our environment.
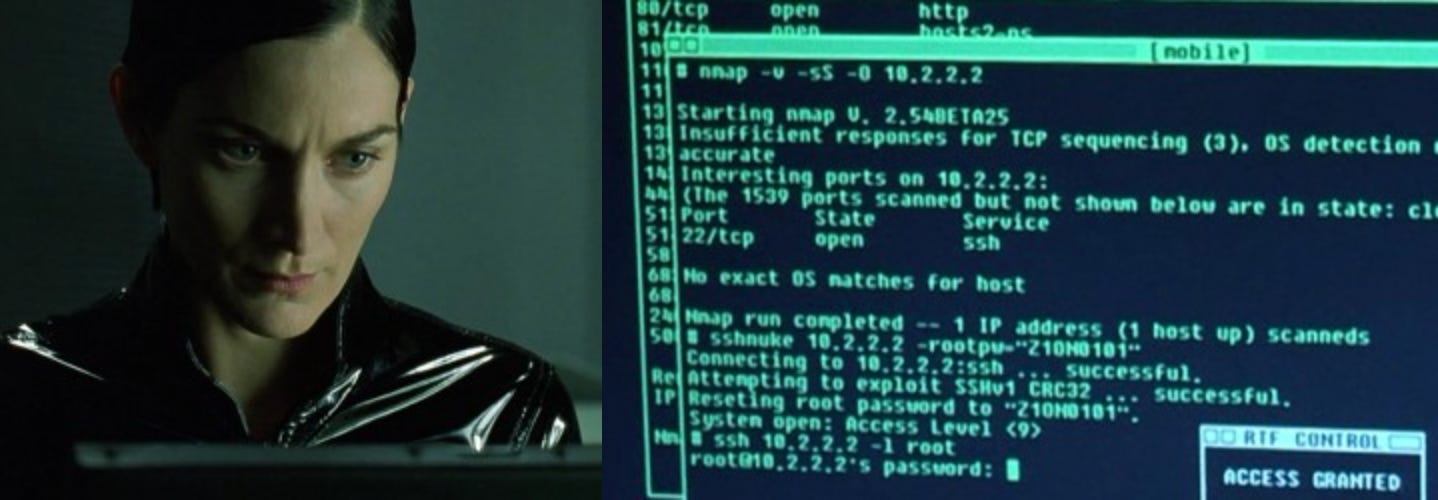
Nmap really is a star, and a movie star, in the realm of cyber tools. It has won a number of awards, is built into a number of operating systems, THE penetration testing framework - Kali Linux, and has been featured in more than 10 movies. Not just any old movies either, some big hits like:
Matrix Reloaded (shown at the top of this post)
The Girl with the Dragon Tattoo
Fantastic Four
Snowden
Die Hard 4
Everything I’ve said here doesn’t even begin to do justice to Nmap and how beloved a tool it is for so many people working in cyber and IT. One immediate benefit attached to that for all of us, is that there are a wealth of great resources online for digging in and learning more about Nmap. The best starting point for that is simple:
If any have stories about your own usage of Nmap, I’d love to hear them in the comments.


Bravo! Nicely written, Patrick! I was originally trained on the green-screen version and never used the GUI one. Too bad, I probably would remember more of the different scan types.
I’m going to use this article as a means to deepen my relationship with our firm’s IT geniuses. I often find myself totally inept when troubleshooting issues with them. Tech and Nonsense has helped pique my interest by laying it out so....linearly(?)
That makes it easy to digest. It doesn’t obfuscate the point with the super technical nuances that I would have no chance of understanding at this stage in my tech education.
This is neat. Movie star 😝😎.