Cybersecurity Tools - Kali Linux
THE penetration testing framework for attackers and defenders
Kali Linux is a genuine legend when it comes to cybersecurity tools, and has a rich history worthy of the legend status. It is an essential tool for cyber attackers, cyber defenders in red and blue teams, and in boot camps and training courses for those looking to master offensive security and penetration testing skills. This post will offer just a brief overview of Kali. It won’t even begin to do it justice, so I’ll share some further resources links throughout.
What Makes Kali Great?
All the Tools for All the Things
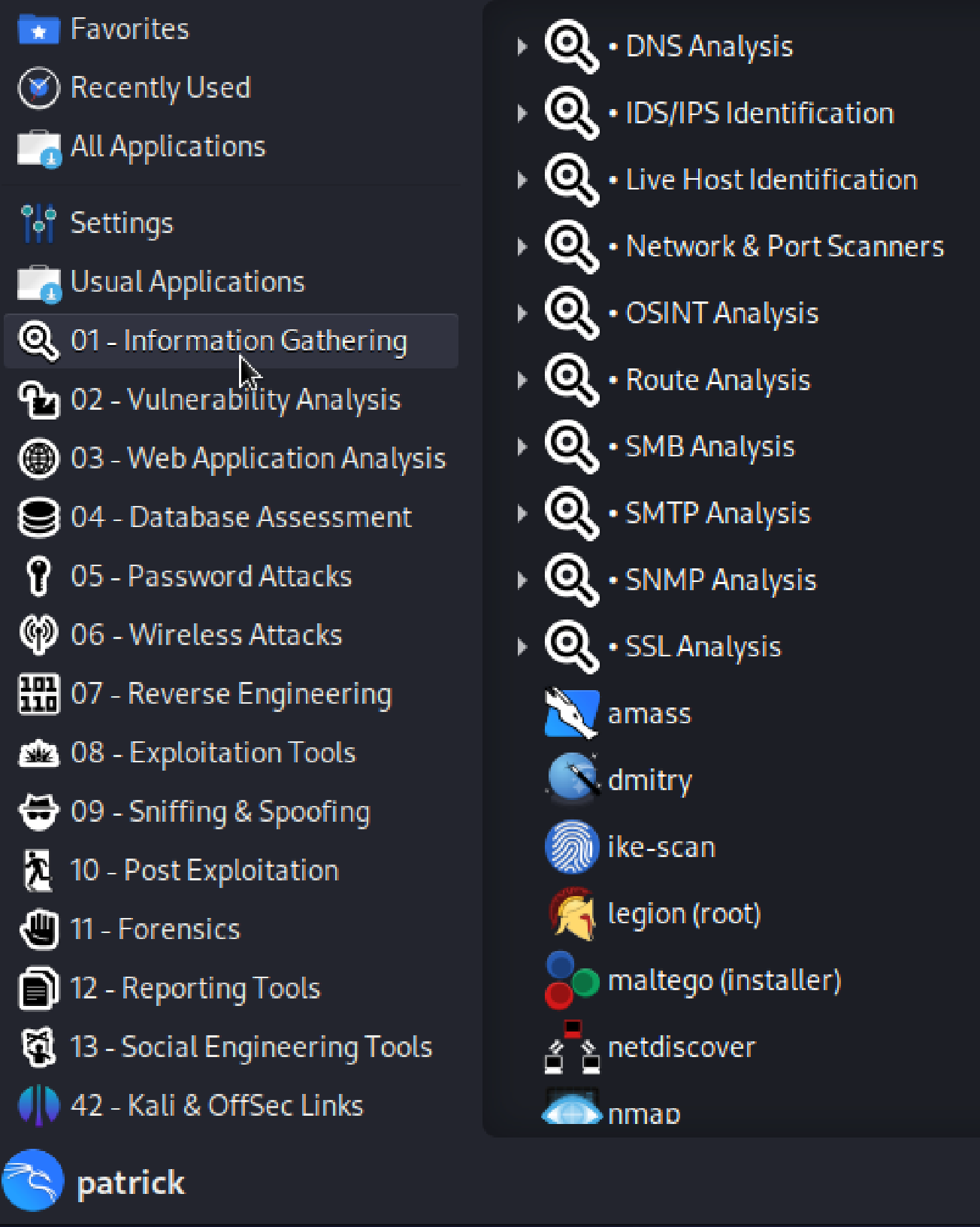
Kali is a penetration testing framework. A jam-packed toolbox of penetration testing tools across a very wide range of categories. There are literally hundreds of individual tools. Here’s a look at the categories listing for some of the most used tools:
Apart from just the broad coverage of these categories of tools, you can also see how they relate to the phases of The Cyber Kill Chain - from Information Gathering (Reconnaissance) to Exploitation Tools (Exploitation), and Post Exploitation and throughout.
Zooming in on the tools listed under Information Gathering starts to give you an idea of the sheer volume of tools included in Kali.
All The Uses for Offense / Defense / Training
Kali is an excellent tool for “black hat” (the bad guys) penetration testers looking for ways to get into a victim environment and pursue their attack goals within it. It is also an excellent tool for “white hat” - not the bad guys, individuals or companies hired to test an organization’s cyber defenses - penetration testers. This sort of exercise is a common best practice used by the cybersecurity blue team to surface ways to exploit vulnerabilities in their environment that have not been uncovered by their own security tools. It’s used in similar ways by cybersecurity red teams to gauge the strengths and weaknesses of people, process, and technologies.
My first brush with Kali was in another area where it has been widely used for many years - training. It was the tool we used in a CEH (Certified Ethical Hacker) boot camp course back in the early 2000s - back when it was not named Kali yet. It was Whoppix and we ran it on live CDs (which now feels like walking with dinosaurs of course). Now it is even more broadly used in training courses - including what feels like the pinnacle of offensive security / penetration testing certifications - the OSCP from Offensive Security.
All the Things You Can Run It On
You can install Kali Linux on bare metal, and it also works wonderfully well as a virtual machine. The screenshots above are from Kali running in a virtual machine on my iMac. You can even run a version of it - NetHunter - on Android smartphones, with its own NetHunter App Store for Android penetration testing and forensics tools.
All the History
Ok, all the history may not feel like it is a practical benefit of Kali - but it speaks to the dedication of the team that built it and the respect and even love for it in the cyber community. And it’s just plain super cool as well. I think just this section of their History page on the dragon logo will give you a flavor for that:
Throughout the projects, one item has been constant. The logo. The dragon. To the point that the logo is potentially better known than the project itself!
What originally started out to be a competition, originating on the Whoppix forum, the idea was “best graphic will be the next wallpaper”. The first submission that was awarded the winner, was the dragon. We liked it so much, we never re-opened the competition for the next version!
What we did not know at the time, was that the submission was plagiarized. It was taken from deviantart without the authors permission. We tracked down the rightful author and bought out the rights to it for Kali Linux.
The design of the dragon has been slightly tweaked over the years, by altering here and there such as making it thinner in places (put on a diet!), curving the tail a little more etc. But we have always been careful to protect the iconic image as it is one of the most recognizable logos in this space. And to answer the question, we have no plans to ever replace the dragon logo.
The origin story for the name Kali is even better. No spoilers here for that - go read this: https://www.kali.org/blog/10-years/#kalis-name. Then check out the full History page too.
Until this morning, I did not know that Kali’s history includes songs about it - and I am very happy that I learned this. I think this is a fine note for this post to go out on …





Wow! Great song and fits the topic for some reason...not sure how or why, but it does. A very interesting article and one that I'm going to have to take a bit of time on, I can tell . I'm betting its worth it though.
another great article, thanks for sharing.