Cybersecurity Terms - Indicator of Compromise
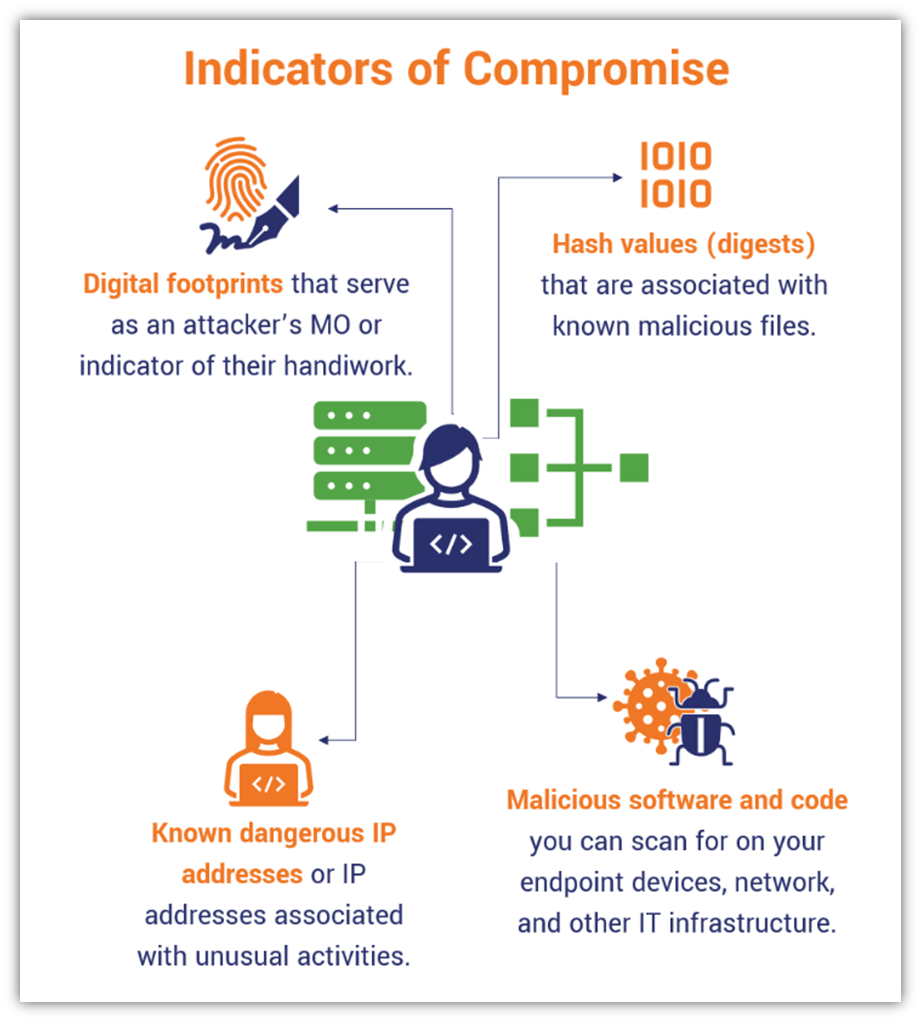
Indicators of Compromise (IoCs) are an essential reference and learning resource for cyber defenders. They can serve to learn from known attacks that have already happened out in wild, to detect attacks at various stages, and to learn from successful attacks that have occurred in our own environment and are then classed as incidents.
An IoC is a piece of evidence indicating that some level of compromise has occurred within our environment. There is a broad - and constantly growing - range of IoCs - that mostly correspond to stages of attacks. They’ll match up well with the Tactics in MITRE ATT&CK for example, from initial access to tactics that look to achieve persistence in the victim environment; move laterally and gain higher levels of access; evade detection; and achieve the end goals of the attack;
So where / how can we find IoCs?
Some IoCs are most easily seen as anomalies - in user account related events, network traffic and so on. Others are very specific details, such as malicious filenames or IP addresses and domains used by attackers.
When there are attacks that impact large numbers of organizations there will typically be detailed reporting on them from government agencies involved in cyber defense and private organizations that provide incident response, Cyber Threat Intelligence (CTI), and general cybersecurity services. Here’s a little slice of a report from Mandiant- showing attacker domains as one of several IoCs - used in a spearphishing campaign a few years ago. These domains are listed as “used for C2” - meaning that the attacker/s use them to push tools into the victim environment and/or exfiltrate data out to their servers in those domains.
The Red Canary Intelligence Insights report for July 2023 includes this section on IoCs for a recently trending information stealing attack:
The IoC details in these sort of external reports can be added to our detection tools - including firewalls, intrusion detection and prevention systems, anti-virus/anti-malware tools, and our Security Incident and Event Management (SIEM) solutions. All of these tools, and our cybersecurity operations engineers and other cyber team members are critical in our efforts to continually improve our ability to detect IoCs at the earliest stage possible.
It’s easy to have a little bit of a doom and gloom feeling about ever evolving attack methods and their associated IoCs. I prefer to stay optimistic and think about how we can strive to do the same as defenders - continually improving our CTI and detection and the overall maturity of our cyber programs and the capabilities of our security tools.






