Cybersecurity Skills - Report Writing
Being able to write a good report is an essential cyber skill
Writing skills is another common topic that comes up when I’m talking with students in the MITxPro Cybersecurity course. In particular, being able to write a good report. I’m generalizing here, which is always dicy, but the reality is that the ability to write a good report is going to be essential in most roles and teams within the cybersecurity department.
This will be true for reports covering a wide range of cyber activities, including penetration tests, cyber risk assessments, security maturity and security controls assessments, red team exercises, threat hunting, and more.
So what does a good report look like?
Structure:
There’s a basic structure that should be a good fit for reporting on the list of activities I mentioned above, and probably beyond those as well. Here’s what that looks like:
Executive Summary
Purpose: This states why we are doing the thing we’re reporting on, what the benefits of doing it are. For example, the purpose of a cyber risk assessment could be defined as delivering data to senior management on the most critical risks the organization faces, enabling them to make risk-based decisions on which risks to accept, avoid, transfer, or mitigate.
Scope: Scope defines what was assessed/included within the activities described in the report. The scope of a threat hunt, for example, might be to confirm or disprove a hypothesis that we can find evidence of an adversary group’s tactics, techniques, procedures (TTPs) within our environment.
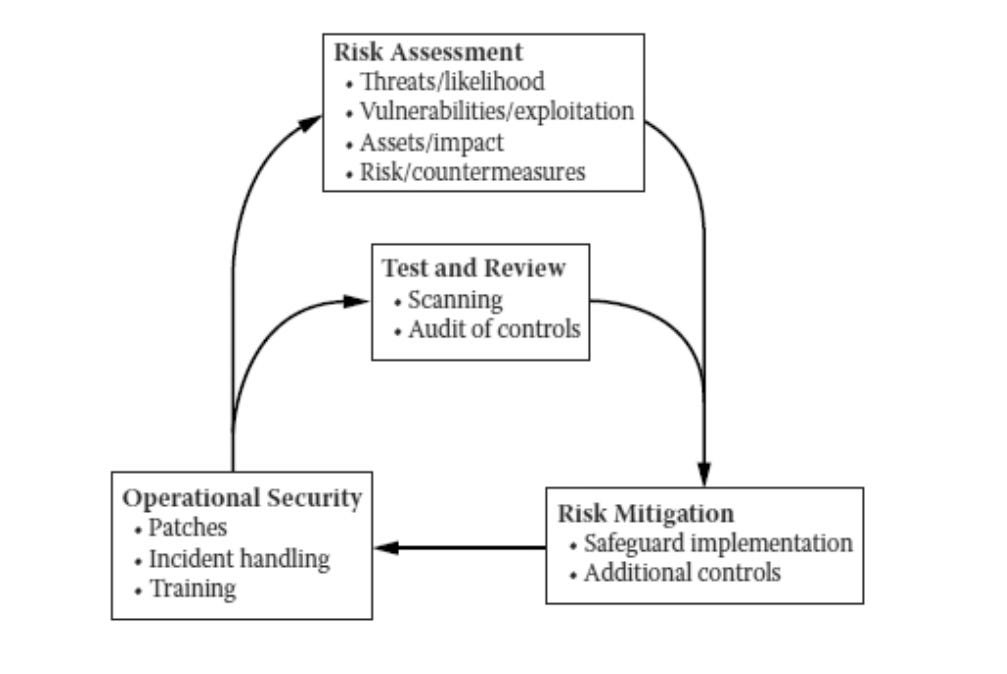
Methodology: This section describes how, for example. our cyber risk assessment was carried out. Diagrams can sometimes help in showing the methods used.
The key word here is summary. This section needs to be short and needs to avoid diving into any of the technical details - otherwise a lot of it will likely not be read or given much attention.
Findings
The findings of the assessment or testing are listed here.
The list may be in table form (as shown above for a very basic looking cyber risk assessment) or with a regular text layout - whichever suits the nature of the findings best.
Findings are typically listed in order of how critical, potentially impactful they are - from the most critical down to the least critical.
Each finding here may be just a finding title and finding category, with a separate section that provides the technical detail of the finding, or all of that information might be presented in one section.
Recommendations
All the types of testing and assessment activities I listed at the top of this post are going to include recommendations on how to address the findings. Examples of what these look like include:
A security controls assessment should identify gap areas and lead to recommendations - often in the form of a System Security Plan (SSP) - to enhance existing controls or implement new controls to address them.
A red team exercise should identify weaknesses in people, process, and technology and lead to collaboration with the blue team to work on appropriate solutions to those.
A security maturity assessment will focus on organizational practices - including the policies, process, and procedures for those practices - and provide details on the ways these can be improved.
Appendices - if needed
Some reports will have an easier reading flow and be easier for readers with different roles (e.g. leadership, system owners, sys admins) to get through if appendices are used. If the technical details for findings are lengthy and/or complex, they may be better presented in a table in an appendix, for example. If a report contains revision history and/or an area where particular stakeholders need to sign off on it, then those may reside in an appendix as well.
Writing Style and Tone
Of course there’s no single style of writing that works best for all cybersecurity reports, or even for cybersecurity reports in general. There are a couple of things to keep in mind that will lead to reports being well received and maybe even increase the chances that they’ll be acted upon though. These are:
Be Clear and Concise - If you can deliver the information needed and highlight the parts that are most useful for all the types of readers in three pages, don’t write ten pages.
Present Data, Not Opinions - Reports will always be strongest if they make the case for addressing gaps or mitigating risks with facts and data. Stating things in a way that feels judgmental or opinionated will most likely lead to doubtful or negative reactions regarding the quality of the report.
Most of the above is based on my own experience in my 20-some years experience in IT and cybersecurity roles. It may not make sense for everyone or for every type of report you’re asked to write - but I hope it may prove useful for some of you.