Cyber Starters - How to Start Getting Hands-on Experience
The good news is there are a number of easy, low budget, ways to start building up your cyber relevant hands-on experience
Along with landing a first interview, getting some hands-on experience can seem like a big challenge if you’re trying to get into a career, or advance your career, in cybersecurity.
It’s probably a lot easier than you think though - as mentioned above there are a number of easy and low cost ways to start building up your hands-on cyber skills. Here’s a short list of some of the things you can do and make use of for these efforts:
Building a Home Lab
I often tell students that I work with that you only need two computers to get your home lab going; one to be the attacker and one as the victim or target. This is of course useful if you want to test your skills at network or vulnerability scanning, or penetration testing. It is also a useful approach for looking at many other areas - for example, working with Windows servers and desktop computers, running two different operating systems (e.g. a Windows machine and a Linux machine), experimenting with network packet capture, and more.
There are two ways to approach having two computers for your lab. They can be two physical computers or one physical computer with two virtual machines as your attacker and target or whichever roles you want to assign to them. With the first option, you’ll just want to have (or get) two decently powered computers that work for your budget.
The second option is usually less expensive. Your one physical machine should have good specs for processors and RAM - the more the better, with RAM 8GB is ok, 16 is better. If you go this route, you’ll need virtualization software - which you will use to create and manage virtual machines. Here a few good options for that:
VMWare Workstation - for Windows
VMWare Fusion or Parallels Desktop for Mac
Virtual Box - Mac or Windows
Virtual Box is free, the others are reasonably priced.
A Word on What Not To Do
Do not try ever try to scan or attack any device or network that you do not own, unless you have explicit (and in writing) permission to do so. This goes for devices in your workplace or out on the internet.
Try Out Some Great Free Tools/Resources
This is just a very compact - far from comprehensive - starter list:
Windows Evaluation versions: Microsoft typically offers 180 day free evaluation versions for at least the current version and most recent past version of their server and workstation operating systems
Linux: The vast majority of Linux distributions are free to use - Ubuntu and Mint are two that are usually very easy for new Linux users to work with
Kali Linux: The most used (and likely best loved) penetration testing framework, with a huge number of tools built-in and ready to go “out of the box”
Nmap: A long-time star and favorite tool for network discovery scanning and security auditing
Wireshark: Another stellar tool that’s been widely used for many years - for network packet capture and protocol analysis
MITRE ATT&CK: If you have any interest in cyber threat intelligence (CTI) or just learning a little about the tactics and techniques used by attackers in real-world attacks, this is THE resource to get to know.
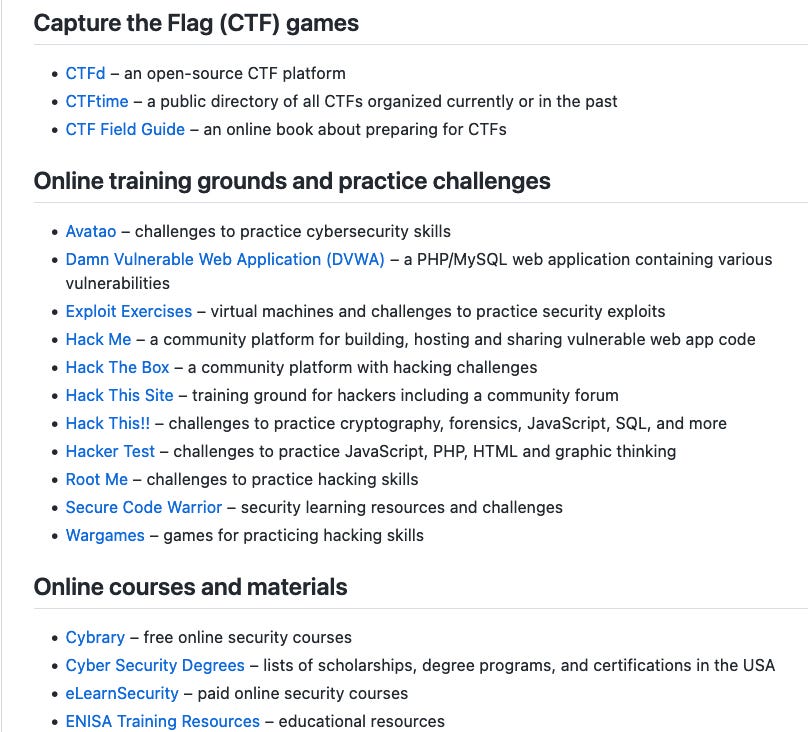
Virtual Labs
There are a huge number of virtual labs to explore online - covering a vast array of cyber relevant areas. You can just use “virtual lab” as your search term to begin to discover these. Add a word or words to drill down to a specific area of interest, for example, “network monitoring”. Here is a very good curated list of sites that are online training grounds for (primarily) trying to hack intentionally hackable computers, along with some free / well-priced cyber training resources: https://github.com/CSIRT-MU/edu-resource
There is a whole lot more you can do in this area, and your options will be continually growing as you’re learning. I hope this short post will serve you well in the early stages of your exploring this area. I would love to hear any questions you have on the things I’ve outlined and how to get them going for you. Please don’t hesitate to ask questions in the Comments here.




Excellent article, Patrick! Well done!
One white paper I discovered a few years ago is a quick and useful resource for someone trying to get started in cybersecurity. The paper is called "Self-Development for Cyber Warriors," and is available at the following link: https://smallwarsjournal.com/index.php/jrnl/art/self-development-for-cyber-warriors
Keep up the great work!! Ernie Hayden