Cyber Links - Threat Hunting Resources
Just a few good lists, people, and places to check out if you're interested in threat hunting
Image Via: Applied Network Defense
Threat hunting is an area within cybersecurity that fascinates me, and an area that I believe has huge value as a part of our cyber defenses. It starts with the notion that no matter how many state-of-the-art security solutions we have in place, none of them are impregnable or bullet proof. At some point, a bad actor / bad thing is going to get past them - and we threat hunt to find those actors and things.
This post was inspired by a very nice list of threat hunting resources published this week by Active Countermeasures: https://www.activecountermeasures.com/threat-hunting-resources/. It’s a short but very useful list of links aimed particularly at “The first few minutes of a threat investigation or incident response …” - ways to get information quickly on ports, IP addresses, domains, potential malware, and more that are seen in the investigation.
Reading that post got me thinking about some of my favorite threat hunting resources - some that have started me on my education on threat hunting, and others that are useful when planning or carrying out a threat hunt. I’ll start by saying there are too many of these to mention here without turning this into TLDR material, but these are a few that are top of mind and most appreciated:
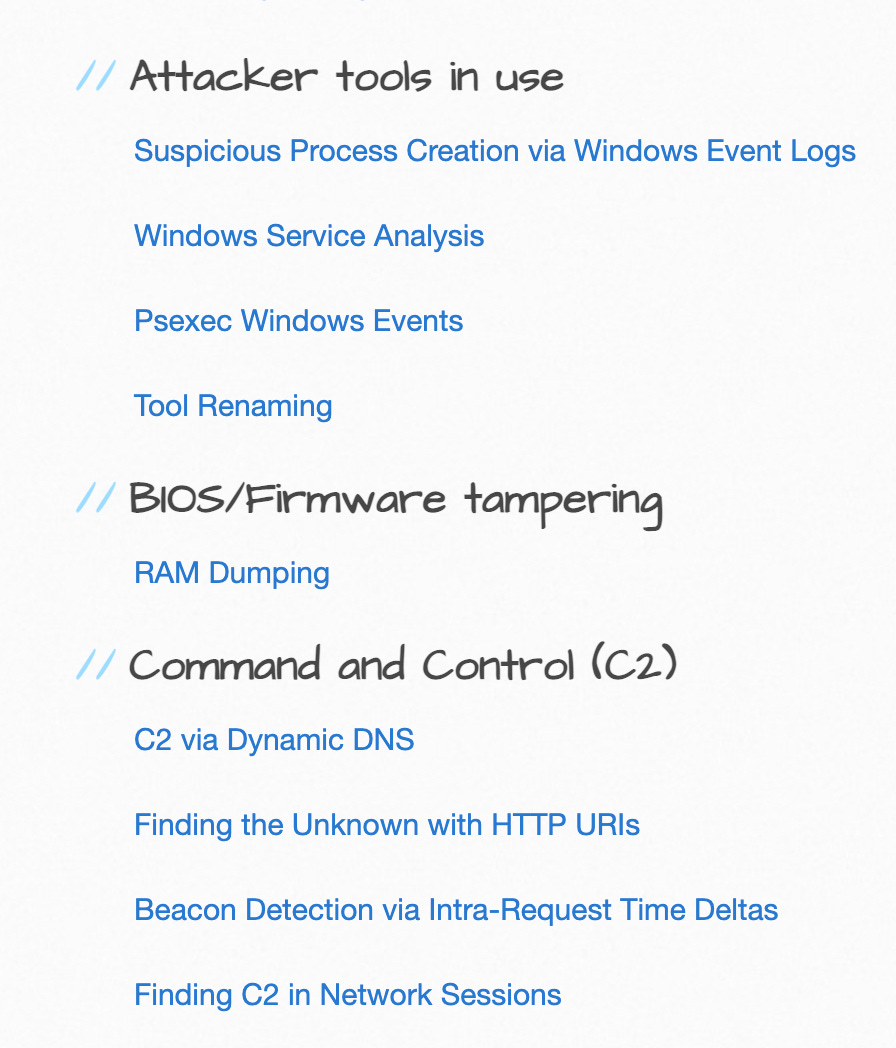
Practical Threat Hunting - A course provided by Applied Network Defense. I’ve been fortunate in being able to take many excellent cybersecurity training courses over the years, many of them paid for by my employers. This course is by far and away my favorite, and more importantly the one I got the most immediate practical use out of. It helped me make some very good headway in building threat hunting profiles, a threat hunting wiki, and a fledgling threat hunting program.
The Threat Hunting Project - This might well be the single best starting point resource if you want to begin learning about threat hunting. The Reading List page is pure gold all on its own. The Hunting Procedures pages are gold, or perhaps even platinum, once you’re actually getting down to doing some hunting. There are lists for Procedures by Goal, and By Data. This project is the creation of David J Bianco, who I think it’s fair to say is a much admired threat hunting guru.
Malware Archaeology Cheat Sheets - The links here are a few years old now, but still very useful. They are Windows focused and include cheat sheets for Windows logs, the Registry, and Sysmon, as well as a couple of MITRE ATT&CK logging links. Which leads me nicely to …
MITRE ATT&CK - I would say that ATT&CK is at least in the discussion for the best single community resource for all of us on the blue team, defensive side of the cybersecurity house. I will not even try to provide a better introduction to it than its own:
MITRE ATT&CK® is a globally-accessible knowledge base of adversary tactics and techniques based on real-world observations. The ATT&CK knowledge base is used as a foundation for the development of specific threat models and methodologies in the private sector, in government, and in the cybersecurity product and service community.
I hope these resources will be interesting and useful for you if you are looking into threat hunting. Please add a comment if you have others you recommend.